When you conduct business online, you often interact with clients whom you have never met. In addition, those clients could be thousands of miles around the globe from where you are. So, how do you confirm they are who they claim to be?
The process of verifying your customer’s identity is referred to as authentication. It is important to authenticate a customer’s identity because there are many malicious cyber actors surfing the web who work quickly and diligently to attain your client’s sensitive data such as personal identifiable information for their own financial gain. How? These actors can hack your user’s email, phone, laptops, tablets, etc.
If the criminals gain access to your customer’s information, it could cause havoc to your online interactions. Your clients could lose valuable investments or confidential data – and your company could then be held liable. The worst-case scenario is that your customers losing all their financial assets.
However, all is not gloom. On the brighter side of things, websites have become more aware of the actions of cybercriminals. These websites are now beginning to require further validation that assures that the clients they are interacting with are who they claim to be. That is where multi-factor authentication comes into play.
What Is Multi-Factor Authentication (MFA)?
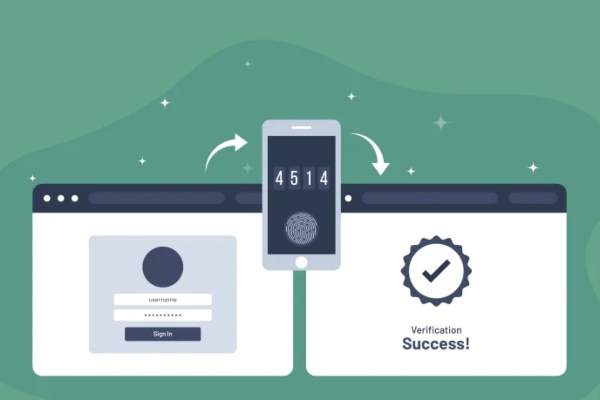
Multi-factor Authentication, or MFA, is an authentication process that requires you to provide two or more verification methods to access a resource such as an online account, application, or a VPN. MFA is a critical component of a resilient identity and access management (IAM) policy. Instead of asking for only a username and password, MFA requires users to provide two or more verification factors. Doing this decreases the possibility of successful cyber-attacks.
How Does MFA work?
One of the most common MFA factors you might encounter is the one-time passwords or OTP. One-Time Passwords are the 4-8 digit codes you receive via SMS, email, or mobile app.
When an application requires an OTP, a new code is generated each time or periodically when an authentication request is submitted. This authentication code is generated based upon a seed value. This value is assigned to you when you first register your MFA device. In addition, MFA might add some additional factors based on time or system-based increments.
Why is MFA Important?
The main advantage of MFA authentication is that it enhances your organization’s online security by requiring users to identify themselves using more than a password and username. While important, passwords and usernames are more susceptible to brute force attacks; making them available to unauthorized third parties. Using an MFA factor like a physical hardware key or thumbprint creates higher confidence that your online organization will remain safe from cybercriminals.
Three Main Types of MFA Authentication Methods
Most MFA authentication processes are based on one of three types of extra information:
- Things you know (knowledge), i.e., a password or PIN.
- Something you have (possession), such as a smartphone or a badge.
- Something you are (inherent), for instance, a biometric like voice recognition or fingerprints.
Examples of MFA
There are many examples of Multi-Factor Authentication. These examples include:
Knowledge
- Answers to your personal security questions.
- Passwords.
- OTPs (This can be both Possession and Knowledge – You know your OTP requirements and need to have something in your possession to access it like your phone).
Possession
- OTPs generated using smartphone apps.
- OTPs sent via email or text messages.
- USB devices, Access badges, Fobs, Smart Cards, or security keys.
- Software certificates and tokens.
Inherence
- Voice, fingerprints, retina or iris scanning, facial recognition, or other Biometrics.
- Behavioral analysis
Other Types of MFA
As MFA integrates artificial intelligence (AI) and machine learning, authentication methods become more complex, including:
Location-Based
Location-based MFA looks at the user’s IP address and, where possible, their geographical location. For example, account-holders can use Location-based MFA to block a user’s access if the location information does not sync with specifications on your safelist. Or the IP was used as an additional form of authentication and different factors such as an OTP or password to confirm your user’s identity.
Adaptive Authentication or Risk-Based Authentication
Another sub-category of Multi-factor Authentication is Adaptive Authentication. This type of authentication is also known as Risk-based Authentication. This approach analyzes additional factors that consider the context and behavior of the user. Often, this method uses such values to assign a risk level associated with the login attempt. For instance:
From what location is your user when trying to access information?
When is the user trying to access your company’s information? Is it during your regular hours or “off hours”?
What kind of device is the user using? Is it consistent with what has been used before?
Is the connection to your website via a public network, or is it through a private network?
The level of risk is calculated based on the answers to these questions. Users can use these answers to know whether the authentication system will prompt them to provide additional authentication factors or allow them to log in. Thus, another term used to refer to this type of authentication is risk-based authentication.
The Difference between Two-Factor Authentication (2FA) and MFA
MFA is used interchangeably with two-factor authentication (2FA), but 2FA is a subset of MFA. Two-factor authentication restricts the number of factors required to confirm the user’s identity to only two elements – MFA, on the other hand, can need two or more components to verify the user’s identity.
Get Reliable Multi-Factor Authentication Services in the Washington, D.C. Metropolitan Area
You should not risk dealing with cybercriminals. Instead, you should install an MFA system on your website or application; this helps you heighten the security of your website and applications and play a major role in protecting your client’s data.
If you need additional help understanding your organization’s MFA requirements or needs, contact NGEN today. NGEN has a credible award-winning reputation in cybersecurity in the Washington, D.C. metropolitan area, and can provide affordable, customized solutions to meet all your IT needs.